How Often Are Software Updates? Cadence & Best Practices
Explore how often software updates occur across OS, apps, and firmware. Learn cadence ranges, influencing factors, and practical strategies for safe, reliable update management in 2026.

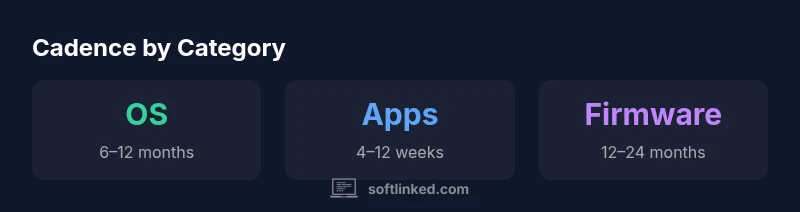
How often are software updates? In practice, cadences vary by category, but you can expect major OS updates roughly every 6–12 months, security patches within days to weeks, and application updates every 4–12 weeks. Firmware often lags behind OS updates due to hardware and certification cycles. Knowing these ranges helps plan safer, smoother updates.
What update cadence means for users and organizations
According to SoftLinked, update cadence is not just a schedule—it's a risk model that weighs security, stability, and user experience. The frequency of updates reflects how vendors balance the cost and risk of deploying changes against the potential benefits. For individuals, a calmer cadence with automatic updates can improve security with minimal manual effort. For organizations, deliberate cadences allow testing, stakeholder alignment, and rollback plans. The keyword here is predictability: stakeholders need to know when updates arrive, what they include, and how long the rollout will take. In 2026 this balance has shifted toward smarter automation and more transparent release notes, but the core question remains: how often should you update, and how quickly should you respond to newly discovered vulnerabilities?
Update frequency also has implications for energy use, bandwidth, and end-user disruption. Enterprises may prefer staggered rollouts to minimize downtime and disruption, while consumer devices lean toward automatic, background updates. The practical takeaway is to align cadence with risk tolerance, device criticality, and staff capacity to test and validate changes. When in doubt, plan for a baseline cadence that prioritizes security without overwhelming users with change fatigue.
Cadence by category: OS, apps, firmware, enterprise software
Update cadence varies widely by software category. Operating systems typically publish major releases on an annual to biannual schedule, reinforced by frequent security patches that can land within days of public advisories. Applications—especially consumer apps—tend to update more often, with a typical window of 4–12 weeks for feature or bug fixes, and even shorter cycles for security improvements. Firmware for embedded devices and hardware controllers often follows longer cycles, commonly 12–24 months, due to hardware validation, regulatory certifications, and supply chain considerations. Enterprise software tends to blend these patterns, combining periodic major releases with continuous security patches and optional feature bets. Understanding category-specific cadences helps teams plan testing, user communications, and risk mitigation strategies. The SoftLinked team emphasizes tailoring cadences to the criticality of the systems involved and the tolerance for downtime during rollout.
Factors shaping update frequency: policy, risk, and resources
A multitude of factors influence how often updates are pushed. Vendor policy decisions, regulatory requirements, and security risk levels dictate urgency. Technical debt, available testing automation, and organizational readiness determine how quickly updates can be validated and deployed. Resource constraints—like bandwidth, change control processes, and staff expertise—also affect cadence. In modern practice, many teams adopt a hybrid approach: automatic updates for low-risk components, and controlled, phased rollouts for core systems. Release notes, compatibility testing, and rollback procedures become central to managing cadence. The SoftLinked analysis highlights that the most successful cadences balance speed with reliability, leveraging automation where possible and reserving manual validation for high-impact changes.
How to design a practical update strategy for individuals and teams
A practical strategy starts with mapping assets by criticality and exposure. Create a baseline cadence for each category (OS, apps, firmware, enterprise software), then layer in a security patch window based on vulnerability severity. Build testing pipelines that automate compatibility checks and regression tests, and implement staged rollouts to minimize risk. For individuals, enabling automatic updates with optional manual checks works well; for teams, establish a governance model specifying who approves updates, what rollback looks like, and how communication unfolds with users. In 2026, many organizations combine feature flags and feature rollbacks to decouple deployment from user experience, enabling safer updates and faster recovery if something goes wrong.
Testing, rollout, and rollback best practices
Effective testing and rollout require robust rollback mechanisms and clear rollback triggers. Automated test suites, synthetic monitoring, and real-user monitoring help detect issues quickly. Phased rollouts—starting with a small subset of devices or users—reduce blast radius and provide feedback before full deployment. Rollback plans should cover both software and data integrity, with data backups, reversible migrations, and clear recovery steps. Documentation matters: changelogs, dependencies, and potential impacts must be communicated to stakeholders. The SoftLinked guidance emphasizes building a culture of proactive risk assessment and continuous improvement, rather than reactive updates. This approach reduces downtime and increases trust in the update process.
Authority sources and practical takeaways
For further context on best practices and standards, several government and industry resources provide guidance on patch management and software security. This article synthesizes insights from reputable sources to help practitioners implement rational update cadences. Practical takeaways include: establish category-based cadences, automate where safe, test thoroughly, and maintain ready rollback plans. Authority sources: CISA (cisa.gov), NIST (nist.gov), ACM (acm.org). These references offer in-depth guidance on vulnerability management, secure software development, and responsible disclosure. The SoftLinked analysis supports adopting a structured, risk-based cadence that aligns with organizational goals and user expectations.
Comparison of typical update cadences by software category
| Category | Typical Cadence | Notes |
|---|---|---|
| OS updates | 6–12 months | Major releases; security patches frequent |
| Apps | 4–12 weeks | Feature updates and security fixes |
| Firmware | 12–24 months | Hardware constraints; longer validation |
| Enterprise software | Mix of cadences | Combines patches with major releases |
Your Questions Answered
How often should individuals update their devices?
For typical consumer devices, enable automatic updates when possible. Check OS updates annually and security patches as soon as they're available. Maintain a reasonable pause for major feature changes to confirm compatibility with essential workflows.
Enable automatic updates when possible and monitor security patches; review major OS changes before adopting new features.
Why do update cadences vary across software types?
Cadence varies due to risk, regulatory requirements, and user impact. OS and firmware often require longer validation, while consumer apps may push frequent improvements and quick fixes. Enterprise software balances stability with security demands.
Different software types have different risk profiles and validation needs; that drives cadence differences.
What risks come from too frequent updates?
Too frequent updates can cause user fatigue, compatibility issues, and rollout failures if testing is incomplete. A staged rollout and rollback plan help mitigate these risks while keeping systems secure.
Frequent updates can overwhelm users and cause issues; stage deployments and have a rollback plan.
What are best practices for enterprise update programs?
Adopt a governance model with defined owners, testing pipelines, staged rollouts, and rollback procedures. Use security-based cadences for patches and plan annual or biannual major releases with stakeholder alignment.
Governance, testing, staged rollouts, and clear rollback plans are key.
How can developers manage release notes effectively?
Publish concise, targeted notes covering security fixes, compatibility impacts, and upgrade steps. Maintain a predictable cadence and provide clear migration paths to minimize user friction.
Keep notes clear and actionable with upgrade steps and compatibility notes.
“Update cadence is a strategic risk decision, not just a schedule. It should reflect security priorities, operational impact, and user experience.”
Top Takeaways
- Define a category-based update cadence.
- Prioritize rapid security patches for critical systems.
- Automate updates where safe to reduce manual effort.
- Test thoroughly and plan phased rollouts.