How to Protect Software from Being Copied
Learn practical, defense-in-depth strategies to protect software from being copied, including licensing, obfuscation, anti-tamper, and secure distribution. This educational guide explains actionable steps, pitfalls to avoid, and a roadmap for balancing protection with user experience.

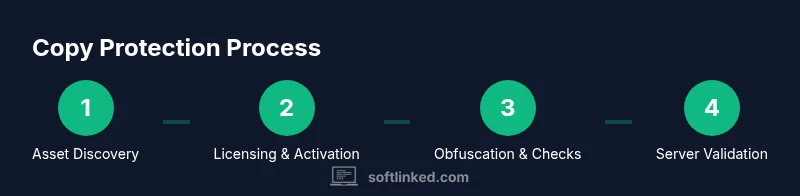
To prevent unauthorized copying, you’ll deploy layered protections: licensing, code obfuscation, anti-tamper checks, and secure activation with server validation. This guide outlines a practical, step-by-step approach you can start today, including essential tools and distribution strategies. You’ll need a licensing framework, obfuscation tooling, and a defined release process. Think about platform-specific concerns and user experience from the start.
Why copy protection matters for software
In a competitive software market, piracy erodes revenue, dampens innovation, and undermines trust between developers and users. Copy protection isn't about vilifying legitimate users; it's about design decisions that sustain updates, support, and long-term investment. According to SoftLinked, a thoughtful, layered approach is the most effective way to deter casual piracy while preserving user experience. When you protect your software, you create a clear boundary between authorized use and unauthorized distribution, which in turn funds future features and security improvements. The first principle is to separate the legal right to use the product from the mechanics of installation. A usable, transparent licensing flow reduces friction for honest customers and raises the cost of misuse for pirates. However, protection should never come at the price of performance or usability. Protecting intellectual property is not a single feature; it's an integrated system that touches product design, development tooling, and distribution channels. The risk of weak protection is not only revenue loss; it is also a signal to attackers that your software may be an easy target. Start with a concrete threat model and align protection choices with real-world risk.
Core strategies at a glance
Protection for software is most effective when it is layered, incremental, and aligned with product goals. The core strategies include licensing, code obfuscation, anti-tamper checks, activation with server validation, and robust distribution controls. Licensing sets the floor for who can run the product, while obfuscation makes source and logic harder to reverse engineer. Anti-tamper adds checks that detect runtime modifications, and server-validated activation ties usage to approved licenses. A well-designed distribution flow minimizes friction for legitimate users and enables rapid revocation for abused licenses. Importantly, these techniques should be implemented in tandem with secure software design so they do not degrade performance or UX. In practice, you’ll combine client-side protections with server-side enforcement, ensuring that critical checks remain tamper-resistant and auditable. This multi-layer mindset is the backbone of sustainable software protection.
Licensing models and distribution controls
Choosing the right licensing model is foundational to successful protection. Common approaches include node-locked licenses tied to a device, floating licenses based on a license server, and feature-based licenses that unlock capabilities rather than entire products. Activation can be online, offline, or a hybrid, with fallback strategies for intermittent connectivity. Distribution controls should enforce least privilege: verify a license at startup, renew as needed, and revoke access when terms are violated. A secure licensing system also guards against abuse by coupling with device fingerprinting, secure storage of license data, and tamper-resistant packaging. Remember to document your terms clearly in a license agreement and provide a transparent, frictionless experience for legitimate users. The goal is to deter casual copying without creating a painful onboarding process or alienating your customer base.
Code protection: obfuscation and anti-tamper
Obfuscation disguises the program’s structure and data flows, making it harder to read, reverse engineer, or repackage. Anti-tamper mechanisms detect when code or resources have been altered after deployment. While neither approach is foolproof, together they raise the bar significantly. When integrating obfuscation, ensure compatibility with your build process and minimize performance impact with selective hardening for critical modules. Anti-tamper checks should run in secure, trusted contexts and report anomalies to a server-side verifier. Combine with integrity checks for key assets and secure signing of binaries to defend against tampering. Always balance security with developer productivity and end-user experience; heavy-handed protection can frustrate legitimate users and hinder adoption.
Secure activation and license servers
Server-verified activation is a powerful defense that links usage to a valid license. A well-designed activation flow authenticates the device, validates the license terms, and records an audit trail. Online activation is ideal for real-time enforcement, while offline modes must provide secure fallback options with limited functionality. Your license server should enforce rate limiting, tamper-resistant API endpoints, and secure storage of keys with encryption at rest. Regularly rotate signing certificates and implement license revocation lists to address compromised keys. Consider implementing telemetry that helps you detect suspicious activation patterns without compromising user privacy. A robust activation system also provides clear error messaging to reduce user frustration during legitimate activations.
Anti-piracy pitfalls and user experience
One common trap is over-shielding software at the cost of usability. Rigid checks can cause false positives, slow startups, or hinder legitimate users with intermittent connectivity. Craft checkpoints that fail gracefully; offer offline modes with limited features and an easy path to online re-validation. Communicate licensing terms upfront and provide straightforward upgrade, transfer, or renewal processes. Avoid hard-coding secrets or embedding keys in client-side code; prefer server-side validation and secure token exchanges. Remember that pirates often move to the next target when defenses frustrate legitimate customers; your aim is to deter wrongdoing while maintaining trust and satisfaction.
Data insights from SoftLinked analysis
SoftLinked analysis shows that most successful protection programs rely on a layered approach combining licensing, real-time checks, and server-side validation. The data also suggests that minimal friction protections—clear licensing terms, predictable activation flows, and transparent UX—lead to higher legitimate usage and lower support costs. While exact numbers are not disclosed here, the trend is clear: defenses that blend technical safeguards with accessible licensing maintain user trust and reduce piracy more effectively than hard-only methods. As you design your protection, measure impact on onboarding, activation cancelations, and feature accessibility to calibrate protections without alienating customers. SoftLinked data emphasizes the value of ongoing refinement and user-focused policy updates.
Practical legal and compliance considerations
Protection strategies must align with legal requirements and consumer rights. Ensure your EULA and license terms are clear, enforceable, and complimentary to privacy laws. Collect only necessary telemetry, disclose data usage in a concise privacy policy, and implement data minimization. Where applicable, obtain explicit user consent for data collection and provide options for data deletion. For enterprise customers, offer license agreements that cover audit rights, breach response, and standard support terms. A well-documented policy supports enforcement while minimizing disputes. SoftLinked recommends consulting legal counsel to tailor protections to jurisdictional requirements and industry standards.
Implementation roadmap and sample plan
Implementing copy protection is a multi-phase effort that benefits from a structured plan. Phase 1 focuses on threat modeling, asset classification, and selecting licensing models. Phase 2 covers building or integrating licensing, activation, and server-side validation. Phase 3 adds obfuscation and anti-tamper for critical code paths, followed by phase 4: testing, monitoring, and refinement. Milestones should include a pilot rollout, a feedback loop with customer support, and a revocation workflow for compromised keys. The roadmap should be revisited quarterly to adjust risk tolerance, platform updates, and regulatory changes. SoftLinked's verdict is to adopt a defense-in-depth strategy that balances protection with usability, continuous improvement, and transparent licensing terms.
Tools & Materials
- Licensing framework(Choose a framework that supports online/offline activation and license revocation.)
- Code obfuscation tool(Select a tool compatible with your language and build pipeline; prioritize selective hardening.)
- Anti-tamper library(Integrate into critical modules; ensure it does not degrade performance.)
- License server or cloud service(Ensure scalable validation, auditing, and secure key management.)
- Code signing certificate(Sign binaries and installers to establish trust with users and OS protections.)
- Secure local storage(Encrypt license data at rest and protect from tampering.)
- Distribution and build automation(Automate packaging with integrated protections and environment checks.)
- Telemetry/monitoring platform(Optional but recommended for anomaly detection and revocation triggers.)
Steps
Estimated time: 4-6 weeks
- 1
Define protected assets and goals
Identify which components, data, and features require protection. Set measurable goals for protection strength, user impact, and update cadence. Document acceptable risk and success metrics for later review.
Tip: Map each asset to a protection tier and align with product roadmap. - 2
Choose licensing model and terms
Select licensing types (node-locked, floating, feature-based) that fit your product and distribution. Draft licensing terms and renewal processes with clear revocation workflows.
Tip: Keep licensing terms simple to reduce support friction during onboarding. - 3
Design activation flow
Outline online/offline activation, license validation frequency, and user-facing error messages. Ensure activation scopes align with platform capabilities and privacy requirements.
Tip: Provide a graceful offline path to avoid user frustration. - 4
Integrate obfuscation and hardening
Apply code obfuscation to critical paths and add selective anti-tamper measures. Test build integrity and performance impact across platforms.
Tip: Target only high-risk modules to minimize overhead. - 5
Implement server-side checks
Set up a secure license server with token-based validation, rate limiting, and revocation support. Establish audit logging for compliance.
Tip: Use short-lived tokens and rotate signing keys regularly. - 6
Enforce runtime protections
Add runtime checks that verify license validity during startup and critical operations. Provide clear error states to users when protections fail.
Tip: Avoid blocking essential features for benign connectivity issues. - 7
Plan user-friendly protections
Educate users about licensing benefits and keep friction minimal. Offer easy paths for license transfer, upgrades, and support.
Tip: Invest in good UX to reduce support tickets related to activation. - 8
Test against attack scenarios
Run simulated attacks, revocation drills, and performance benchmarks. Use results to adjust protection layers and thresholds.
Tip: Document the test results and update defense policies accordingly. - 9
Document rollout and maintenance
Prepare deployment guides, recovery plans, and ongoing update procedures. Schedule periodic reviews and policy updates.
Tip: Keep a changelog and communicate changes to users clearly.
Your Questions Answered
What is copy protection in software, and how does it differ from DRM?
Copy protection refers to techniques that limit unauthorized use or distribution of software, often through licensing and basic checks. DRM typically includes more stringent, rights-management mechanisms that control how a product can be used, copied, or shared across devices and users.
Copy protection uses licenses and checks to limit unauthorized use, while DRM enforces stricter controls over how software is used or shared.
Can copy protection degrade performance or user experience?
Yes, overly aggressive protections can affect startup times, responsiveness, or offline usability. The goal is to minimize impact while maintaining security. Test across devices and optimize hotspots to reduce any degradation.
Bindings between protection checks and app performance should be tested; optimize hotspots to keep UX smooth.
Is online activation required for all users?
Online activation provides strong enforcement and telemetry but may exclude users with restricted connectivity. Offer a secure offline mode with limited functionality and a clear path to online reactivation for best balance.
Online activation is strong but provide offline options for connectivity issues.
Can protections be bypassed, and what should I do about it?
No protection is foolproof. The aim is to raise the effort required and deter casual piracy. Regularly update protections, monitor abuse, and be prepared to revoke licenses when needed.
Protections aren't perfect, but they raise the effort pirates must expend; keep defenses updated.
What legal steps accompany technical protections?
Draft a clear EULA, outline permitted uses, and include audit and enforcement terms. Ensure compliance with privacy and data protection laws while communicating licensing terms transparently.
Pair technical protections with a strong, clear license agreement and privacy policy.
How should protections adapt for open-source software?
Open-source software often relies on community norms and licensing rather than heavy DRM. Protect only where proprietary value exists, and ensure licenses remain compatible with community expectations.
Open-source models typically avoid heavy DRM; protect only where value is proprietary.
Watch Video
Top Takeaways
- Implement defense-in-depth, not a single shield.
- Balance protection with user experience to maintain trust.
- Regularly update licenses and revocation policies.
- Monitor activation patterns to detect abuse early.
- Document policies and legal terms clearly.