How to Install Software Without Admin Passwords
Learn safe, compliant strategies to install software without admin passwords, including portable apps, per-user installations, and how to request privileges when needed for legitimate workflows.

There is no legitimate way to install software without admin credentials on managed systems. This guide outlines safe, compliant options: portable apps, per-user installations, and requesting privileges when needed. You’ll learn step-by-step methods, how to evaluate software sources, and how to document your process. We emphasize legal pathways, security considerations, and collaboration with IT.
Why admin passwords matter in software deployment
According to SoftLinked, admin passwords and elevated rights exist to protect endpoints, data, and user experiences from accidental or malicious changes. On many managed devices, the question of how to install software without admin password is addressed through approved workflows rather than shortcuts. The SoftLinked team found that bypass attempts often trigger security alerts, violate policy, and can leave systems vulnerable to malware or misconfigurations. This is why understanding the why behind elevation helps you choose compliant paths rather than risky hacks. In practice, software installation touches several layers: system permissions, security software, installer wrappers, and asset inventories. When you attempt to circumvent controls, you may disable protections that defend against phishing, supply-chain compromises, and unauthorized software. The goal of this section is to set expectations: you should seek legitimate routes, document the decision, and align with your organization’s security posture. If you encounter a blocker, pause, escalate, and pursue a documented process for obtaining permission or an approved alternative. The remainder of this article walks you through safe, practical options.
Safe, legitimate strategies to install software without admin password
There are several safe paths you can take that avoid policy violations while still solving a real need. First, explore portable versions of software that run from your user profile or a removable drive without touching system folders. Second, look for per-user installation options offered by the vendor, which install only in your home directory or user sandbox. Third, choose web-based or SaaS alternatives when possible, since they run in the browser or cloud without local installs. Fourth, engage your IT or security team to obtain temporary or Just-In-Time privileges for a sanctioned install. Fifth, use virtualization or sandbox environments to assess software before requesting a formal deployment. By combining these approaches, you can complete many tasks without compromising device integrity or policy compliance. Always document decisions, confirm digital provenance, and respect blackout periods or change windows defined by your organization.
Portable apps: run apps from your user profile
Portable applications are designed to operate without a formal system install. They store their data within their own folder and do not modify critical system directories. For students and professionals, this means you can carry a suite of tools on a USB drive or a local folder and launch them directly from your user space. When selecting portable options, prioritize publishers who sign their binaries, provide checksums, and offer an official portable variant. Examples include lightweight editors, browsers, and utility tools that advertise a portable mode. Keep in mind that not all software ships in portable form, and some features may require additional components. If a needed program isn’t available in portable form, move to the next strategy in this guide and request a sanctioned install through the proper channel.
Per-user installers and local user spaces
Some software vendors offer per-user installers that place programs into the current user’s directory rather than the system-wide Program Files folder. This approach reduces the need for administrator rights and keeps your footprint contained. On Windows, this can appear as an “Install for me” option or a flag like --user; on macOS and Linux, you may install into ~/.local or a similar user-writable path and adjust PATH accordingly. Before attempting, verify the installer options in the vendor’s documentation and test in a non-production profile. If an installer explicitly requires elevated rights, switch to a portable variant or arrange a sanctioned install instead. Documenting the exact steps you took helps support teams reproduce your environment later.
Linux-focused approaches: user-space installation and local bins
Linux environments often allow user-space installations that do not require root access. You can install software into your home directory using methods like compiling into ~/.local, or using language-specific package managers with a --user or --prefix option. For example, many languages support a per-user installation location that hands you a private bin directory on PATH. After installation, update your PATH in your shell profile so you can run the new programs without sudo. When a program depends on system libraries you don’t control, look for static builds or consult your IT policy about acceptable workarounds. The overarching message is: where possible, keep software in your own space to protect the device and stay compliant.
Windows-specific options: local installers and virtualization
On Windows, some publishers offer per-user installers that avoid administrative prompts by targeting the user’s app data or local app folders. If the vendor provides a true per-user install, choose that option. When not available, consider sanctioned alternatives like web apps or portable versions. For more advanced testing, you can use sandboxing solutions to evaluate software without touching the main OS. Note that sandbox environments themselves may require initial setup by an administrator, so coordinate with IT. Always follow change-management procedures and never use workarounds that bypass security controls.
How to work with IT security policies
The safest path often begins with a policy-aligned conversation. Reach out to your IT or security team to explain the business need, provide risk assessments, and request a temporary elevation or a documented exception. Create a ticket that includes the exact software name, version, install location, and any restrictions. If approved, perform the installation in a controlled window and log any changes. This approach not only keeps you compliant but also builds a traceable history for audits and future requests. The goal is to establish a repeatable, approval-based process rather than ad-hoc attempts.
How to evaluate software sources safely
Any software you install should come from trusted sources. Start at the publisher’s official site or a well-known repository, verify digital signatures or checksums, and scan the installer with up-to-date antivirus tools. Avoid untrusted download mirrors or torrents. If you’re using a portable version, confirm that the vendor maintains integrity checks and post-install validation steps. Document the provenance of the software and keep receipts of approvals. These practices reduce risk and support a transparent, auditable workflow when you need to expand capabilities on a managed device.
Troubleshooting and next steps
If you encounter roadblocks, re-check policy documentation and confirm the exact install scope allowed for your user, before escalating. Common issues include missing dependencies, blocked network access, and conflicts with security software. When in doubt, pause and return to the approved channels rather than attempting a risky bypass. Once you have a sanctioned path, proceed with careful testing, populate a change-log, and prepare a short report for stakeholders. By following these steps, you’ll transform a potentially fraught request into a smooth, policy-compliant deployment.
Tools & Materials
- Portable software package (portable app)(No admin rights required; store in user profile or on a USB drive)
- Vendor per-user installer option(Check for --user, or Install for current user settings)
- Web-based or cloud alternative(No local install needed; ensure data policy compliance)
- Documentation of IT policy(Keep a copy of policy or change ticket)
- Sandbox/VM or isolated testing space(Safe environment for testing before production)
- Internet access(Needed to download portable or per-user installers)
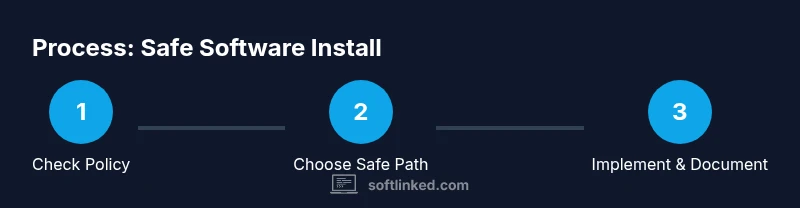
Steps
Estimated time: Total time: 2-4 hours
- 1
Assess policy and seek consent
Review your organization’s policy on software installation and confirm you have written approval to proceed. If your environment requires a formal ticket, prepare the business justification and version details. This step prevents future audits from flagging non-compliant activity.
Tip: Document the approval and timestamp it for future reference. - 2
Identify safe install options
Search for portable versions, per-user installers, or cloud-based alternatives from the vendor or trusted repositories. Prioritize options that do not modify system-wide folders or require elevated rights. If multiple options exist, pick the one with the least risk and easiest maintenance.
Tip: Always verify source authenticity before downloading. - 3
Test in a non-production space
Set up a sandbox or user-space environment to evaluate the software’s behavior and dependencies without impacting critical systems. Validate basic functionality, data paths, and security prompts in this isolated setting.
Tip: Document results and any deviations from expected behavior. - 4
Attempt a per-user or portable install
If a true per-user installer is available, use it and monitor its effects. If using a portable app, extract to a user-writable directory and run from there.
Tip: Avoid system-wide changes unless explicitly approved. - 5
Consider web-based alternatives
If the software’s functionality can be met via a browser or SaaS, choose that path to fully avoid local installation. Ensure data handling aligns with policy and compliance requirements.
Tip: Assess feature parity before switching to web apps. - 6
Request temporary elevation when needed
If the task requires elevated rights, initiate a formal request for Just-In-Time access with a defined window and rollback plan. This keeps your action auditable and compliant.
Tip: Prepare a concise justification and an estimated duration. - 7
Install in approved environment
Perform the installation within the sanctioned window, following documented steps precisely. Maintain logs of actions, versions, and locations for future reference.
Tip: Double-check the installation path and PATH variables if needed. - 8
Document the process
Record the software name, version, install method, location, and any post-install configurations. Share the documentation with your team and IT for reproducibility and audits.
Tip: Include screenshots or logs where helpful. - 9
Review and improve
After completion, review whether policy gaps exist or if a more efficient pathway is available for similar requests. Update internal guides to reflect lessons learned.
Tip: Turn insights into improvements for future requests.
Your Questions Answered
Is it legal to install software without admin password on a managed computer?
In most managed environments, installation without admin rights is not permitted. Always consult IT and follow approved workflows. If in doubt, seek an official exception.
Generally not allowed; check with IT and follow the approved process.
What are portable apps and how do they work?
Portable apps run from a user-writable folder and do not require a system-wide install. They help avoid admin prompts but may lack some features and require careful source verification.
Portable apps run from your folder and don’t install system-wide.
What should I do if something requires admin rights?
Request temporary elevation through the proper IT channel, supplying a clear justification, expected duration, and safe usage guidelines.
Ask IT for temporary access with a clear reason.
Can cloud-based alternatives replace local installs?
Yes, when feasible, web apps or SaaS can meet needs without local installs, while meeting security and data policies.
Consider web apps if local install isn’t essential.
What safety checks should I perform before running new software?
Verify the publisher, confirm digital signatures or checksums, and run a malware scan before execution.
Check publisher and signatures, then scan for malware.
Watch Video
Top Takeaways
- Follow policy and obtain approvals before any install
- Prefer portable or per-user options to minimize risk
- Test in a sandbox and document results for audits
- Verify publisher integrity and avoid untrusted sources
- Document changes and request improvements to policies