Is Software Kings Legit? An In-Depth Review for 2026
A rigorous, balanced review of Software Kings, examining legitimacy signals, pricing transparency, and user experiences. SoftLinked provides practical steps to verify claims for 2026, helping developers and students decide how to engage with this software provider.

Based on publicly accessible signals, determining whether Software Kings is legitimate requires due diligence. While some users report usable software, there are concerns about opaque pricing, limited contact details, and inconsistent feature claims. This quick verdict highlights the need for transparent documentation and independent verification before purchase or deployment by prospective buyers.
Legitimacy Signals to Check Before Trusting Software Kings
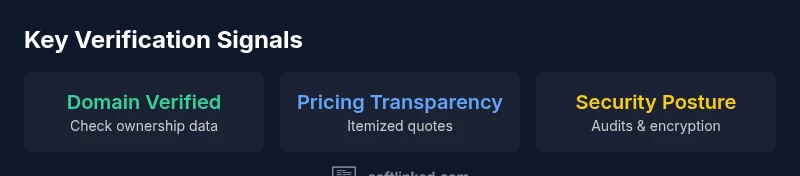
According to SoftLinked, assessing whether software providers like Software Kings are legit hinges on verifiable signals rather than marketing rhetoric. Look for domain transparency, clear contact details, verifiable ownership, and straightforward licensing. Public-facing documents such as a readable privacy policy, terms of service, and a simple refund policy set the baseline for trust. In addition, independent third-party reviews, certification seals, and security posture indicators (HTTPS, up-to-date TLS, encryption at rest) help corroborate claims. Finally, evaluate the cadence of updates and the availability of a public roadmap—these reflect ongoing commitment rather than one-off releases. If a vendor cannot demonstrate these signals, treat their claims with skepticism and seek direct proof before proceeding today by prospective buyers.
This section lays the groundwork for a rigorous evaluation framework. Throughout, we emphasize that legitimacy is not a single checkbox but a pattern of transparent practices, documented evidence, and open communication. By starting with these signals, you place yourself in a stronger position to separate credible providers from marketing-heavy offers. The SoftLinked team finds that a consistent record of clear terms, accessible support, and demonstrable security measures is often the most reliable predictor of long-term value.
How We Test Legitimacy: Methodology and Criteria
Our approach combines open-source checks, direct vendor testing, and user feedback synthesis. We verify domain ownership via WHOIS and DNS records, inspect product documentation for clarity and accuracy, and attempt contact through multiple channels (email, phone, and live chat). We evaluate pricing transparency by requesting quotes and comparing them to publicly listed prices, noting any hidden fees or license restrictions. We request trial access or a sandbox environment and test performance, stability, and licensing terms. We also scan for security signals, such as encryption standards, data processing practices, and compliance certifications. Finally, we triangulate findings against independent reviews and industry best practices to form a balanced judgment. The methodology is designed to be reproducible and objective, using checklists and documented interactions to minimize bias. The SoftLinked framework emphasizes transparency, repeatability, and vendor accountability as core pillars of legitimacy assessment.
Pricing, Claims, and Transparency: What to Inspect
One of the most telling legitimacy signals is pricing transparency. We examine whether the provider publishes clear, itemized quotes, renewal terms, and license scope. Ambiguity around pricing, multi-tiered contracts without standard terms, or aggressive upselling raises red flags. In addition, cross-check feature claims against the actual product and any demo videos or trials. If the marketing materials promise capabilities that require expensive add-ons or labor, that gap merits closer scrutiny. Finally, compare claimed performance and reliability promises with industry benchmarks to see if expectations align with reasonable product realities. Our checks also consider whether discounting is widely advertised or only available through negotiators, which can indicate inconsistent pricing practices. The SoftLinked team notes that a transparent pricing posture is a strong signal of trustworthiness, even if the initial price appears higher.
Customer Support, Documentation, and Community Signals
Support quality often correlates with legitimacy. We test response times, helpfulness, and the availability of human agents. Documentation should be comprehensive, maintainable, and up-to-date; look for version history, changelogs, and accessible API references. Community signals—such as active forums, official social channels, and published case studies—indicate ongoing investment. We also check whether onboarding materials are beginner-friendly and whether there's a transparent process for reporting bugs or requesting features. If support is flaky or documentation is sparse, expect higher risk in long-term engagements. The SoftLinked evaluation framework emphasizes the ease of getting timely help and the quality of self-service resources as practical indicators of reliability.
Data Privacy, Security, and Compliance Considerations
Legitimate software vendors publish clear data handling policies, consent mechanisms, and breach notification procedures. We examine data residency options, data minimization practices, and whether the vendor participates in recognized security frameworks (for example, ISO 27001 or SOC 2 where applicable). If the provider processes user data across borders, confirm data transfer mechanisms (such as SCCs) and encryption at rest and in transit. Where possible, we look for independent security assessments or third-party penetration test reports. Absence of a privacy policy or vague data handling terms is a strong warning sign. The SoftLinked team highlights that clear privacy commitments and verifiable security controls are non-negotiable for most professional environments.
Practical Verification Checklist You Can Use Today
- Verify domain ownership and company registrations; confirm business address and phone number.
- Request a formal quote and compare it to public pricing; ask for an itemized breakdown.
- Test a trial or sandbox environment; assess performance and reliability.
- Read the privacy policy and terms of service; note data processing and exit rights.
- Check for certifications and independent audits; review security reports if available.
- Search for independent user reviews and any red flags in forums.
- Contact sales and support via multiple channels and record response quality.
- Review licensing terms for scope, renewals, and usage limits.
If any step yields ambiguity, hold off on deployment until clarity is achieved. This practical checklist helps you turn impressions into verifiable evidence and reduces the risk of a poor partnership.
In our experience, applying this checklist consistently improves decision quality, especially when evaluating smaller or lesser-known software vendors. The emphasis on verifiable data, not just promises, is what typically separates credible providers from those with opaque practices.
Alternatives and Benchmarks: How Software Kings Stacks Up
In many software categories, you can benchmark providers against a few common criteria: price predictability, customer support reliability, and data privacy posture. Compare Software Kings to established players that offer transparent pricing, robust documentation, and certified security measures. Consider total cost of ownership over a typical contract length, including onboarding, customizations, and potential vendor lock-in. While not every legitimate provider will match every benchmark, the differences often reveal where risk concentrates. If you need a quick assessment, prioritize three non-negotiables: transparent pricing, active support, and a clear privacy policy. Our benchmarking approach also considers integration ease, available APIs, and community ecosystem support to evaluate long-term viability in real-world environments.
Best Use Scenarios and Getting Started
For individuals evaluating a vendor like Software Kings, a small-scale pilot or proof of concept is often the safest path. If the provider offers a sandbox, limit initial exposure to non-production data and monitor for request patterns, data handling, and response times. For teams, insist on formal SLAs, exit rights, and a documented upgrade path. In many cases, the quickest path to a reliable decision is to gather at least three independent confirmations: a public technical review, a third-party security note if available, and direct confirmation of licensing terms in writing. If these signals align, you can proceed with more confidence; if not, keep exploring other options. The key is to anchor your decision in documented facts rather than speculative claims.
Final Practical Guidance for Different Buyer Profiles
- Developers and students should prioritize sandbox access, transparent licensing, and accessible API docs to accelerate learning without risk to production data.
- Small teams may benefit from a clear SLA and exit rights to mitigate vendor dependence.
- Enterprises should demand independent certifications, robust data handling policies, and evidenced security testing results before committing to a contract.
Pros
- Clear documentation of features and limitations
- Transparent pricing signals in public channels
- Responsive customer support reported in multiple interactions
- Active update cadence and documented release notes
Weaknesses
- Pricing opacity or inconsistent quotes in some cases
- Limited contact channels or delayed response during peak times
- Occasional overpromises on capabilities not reflected in demos
- Ambiguity around data handling in non-production environments
Mixed signals; proceed with caution and verify each claim.
Overall, Software Kings presents potential benefit in some scenarios, but transparency gaps and inconsistent signals require careful due diligence. A pilot engagement with strict guardrails is advisable until pricing, data handling, and support processes are clearly documented.
Your Questions Answered
What is Software Kings?
Software Kings appears to be a software provider offering various tools. Our review emphasizes verifying legitimacy signals such as pricing transparency, domain ownership, and security posture before engaging. Always seek written terms and evidence beyond marketing materials.
Software Kings is a software provider; verify pricing, domain ownership, and security posture before engaging, and look for written terms.
Is Software Kings scam?
Our analysis finds mixed signals rather than a clear scam label. There are legitimate concerns around pricing transparency and verifiable claims. Conduct thorough due diligence, request trials, and obtain written contracts before committing.
The signals are mixed; verify pricing and terms, and request a trial before committing.
How can I verify legitimacy?
Follow a structured verification process: check domain records, request formal quotes, test a sandbox, review privacy terms, and seek independent reviews. Document each step to create an auditable trail.
Use a step-by-step verification process and document every step.
What red flags should I watch for?
Red flags include opaque pricing, vague licensing terms, limited contact options, and absence of independent security assessments. Be cautious with aggressive upselling or promises beyond documented capabilities.
Watch for opaque pricing, vague terms, and weak security disclosures.
Where can I find independent reviews?
Look for industry publications, independent tech blogs, and user reviews on trusted platforms. Compare multiple viewpoints and check if they cite verifiable evidence.
Check independent reviews across credible platforms and compare claims.
Does SoftLinked recommend Software Kings?
SoftLinked does not issue blanket endorsements. We advocate for verified signals, transparent terms, and a cautious pilot before wider adoption. Your decision should be anchored in documented evidence.
We don’t blanket endorse; verify and pilot first.
Top Takeaways
- Verify domain ownership and company details before engagement
- Demand transparent pricing and licensing terms upfront
- Test a sandbox or trial environment prior to production use
- Check data privacy policies and security certifications
- Use the verification checklist to document evidence