Why Keeping Software Up to Date Matters for Security
Learn why it is important to keep software up to date, covering security benefits, performance gains, compatibility, and practical steps for teams and individuals.
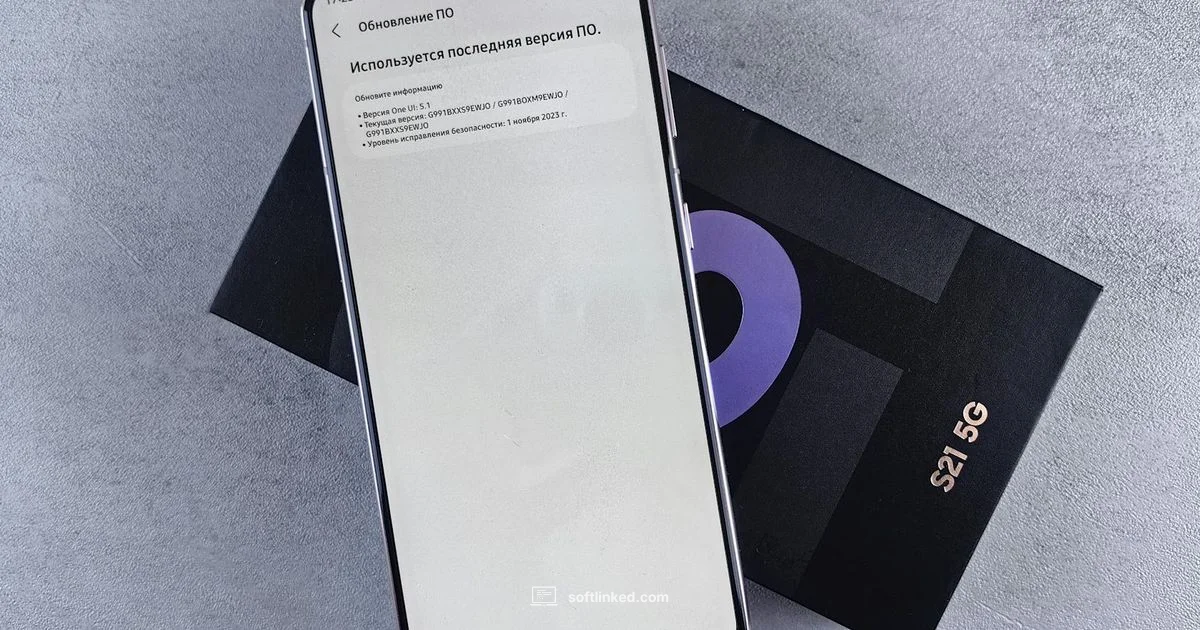
Software updates are a type of software maintenance that patches bugs, closes security vulnerabilities, and improves performance and features.
Why Keeping Software Up to Date Matters
Keeping software up to date is foundational for any modern technology stack. In practice, updates deliver more than new features; they patch security holes, fix bugs that cause crashes or data corruption, and improve compatibility with other software and services. For developers and IT teams, a deliberate update habit reduces the blast radius of outages and accelerates onboarding for new tools. The SoftLinked team emphasizes that a consistent update discipline helps organizations maintain predictable behavior across environments, from development to production. This is not just about reducing risk; it is about enabling teams to move quickly with confidence, knowing that the core software foundation remains secure and reliable.
Key ideas to remember:
- Updates fix vulnerabilities that attackers can exploit.
- Regular updates improve stability and reliability.
- Staying current keeps features compatible with other systems.
- A clear process lowers the chance of failed updates and downtime.
For individuals, automating updates where possible and scheduling periodic checks can make the habit effortless. For teams, embedding update checks into CI pipelines or release cadences helps synchronize effort and avoid last minute surprises.
Security Benefits of Updates
Security is the primary reason many organizations prioritize updates. Vendors release patches to close known vulnerabilities, remove exploitable conditions, and harden configurations against common attack patterns. Unpatched software is a prime entry point for malware, ransomware, and data breaches. Regular updates also improve defense-in-depth by addressing recently discovered flaws across layers—from operating systems to applications and libraries. The SoftLinked analysis shows that many incidents begin with outdated components, underscoring the need for a proactive patching mindset. By applying updates promptly, organizations reduce exposure windows and limit the window attackers have to exploit weaknesses. This alone dramatically changes the risk profile of daily operations.
Practical steps:
- Treat critical patches as non negotiable with clear ownership.
- Prioritize updates based on vulnerability severity and exposure.
- Verify integrity and test critical changes in a staging environment before broad rollout.
- Maintain an inventory of patched versus unpatched assets to monitor progress.
Performance and Stability Improvements
Beyond security, updates frequently improve performance and stability. Bug fixes reduce crashes, memory leaks, and incorrect behavior that can degrade user experience. Performance enhancements might optimize startup times, response latency, or resource usage, which translates into faster software and better productivity. In some cases, updates consolidate improvements to reduce power consumption, extend battery life, or lower operational costs in data centers. For developers, these enhancements can enable new workflows or simplify maintenance tasks. For end users, smoother operation and fewer errors translate into a more trustworthy toolset. Tracking before-and-after metrics can help teams quantify the impact of updates and communicate value to stakeholders.
Actionable tips:
- Run performance baselines before deploying updates.
- Use feature flags to enable changes gradually and assess impact.
- Monitor user reports after updates to detect subtle regressions quickly.
- Schedule regular maintenance windows to avoid surprise outages.
Compatibility and Dependency Management
Software rarely exists in isolation. Updates can affect dependencies, plugins, or integrations that rely on specific versions. A change in one component may ripple across an ecosystem, causing compatibility issues if not coordinated. To reduce surprises, maintain a formal dependency management policy and test updates against critical integration points. This includes operating system versions, runtime environments, and API contracts. In open source environments, governance and contribution practices help ensure compatibility while allowing rapid iteration. The key is to strike a balance between timely updates and careful validation so that new versions do not break essential workflows.
Best practices:
- Maintain a bill of materials for all dependencies.
- Establish a testing matrix that covers core use cases and integrations.
- Use staging environments that mirror production for update validation.
- Communicate planned changes to users and stakeholders to manage expectations.
Risks of Skipping Updates
Delaying updates introduces a range of risks, from minor compatibility quirks to severe security breaches. Unpatched software can expose known vulnerabilities, while outdated drivers or firmware can create instability or data loss. Vendors often discontinue support for older versions, leaving you without critical bug fixes or security advisories. Skipping updates also complicates audits and compliance, as many standards require baseline hygiene of patched systems. The most common consequence is a higher total cost of ownership from preventable outages and remedial work. A disciplined approach to updates, including safe rollouts and rollback plans, helps mitigate these risks.
Key warnings:
- Outdated software is a frequent target for automated attacks.
- Support wind-downs can leave systems without security advisories.
- Patch failures can cascade into business disruption if not planned.
How to Implement an Effective Update Policy
An applied update policy turns a potentially chaotic practice into a repeatable routine. Start with discovery: inventory all software, versions, and update channels. Next, categorize updates by severity and business impact. Build testing and pilot phases to validate compatibility before broad deployment, and establish a rollback plan should issues arise. Schedule updates during low-usage windows and monitor post-deployment health. Documentation and communication are essential so team members understand what changes occurred and why. Finally, automate where safe, with human oversight for high-risk systems.
Practical framework:
- Create a quarterly or monthly patch calendar aligned with vendor advisories.
- Segment assets by criticality and apply different update cadences.
- Implement automated checks for update success and rollback readiness.
- Capture lessons learned after each cycle to improve future runs.
Practical Tips for Individual Users and Teams
Whether you are an individual developer or part of a larger IT department, practical habits matter more than perfect execution. Enable automatic updates where feasible, and set aside regular times to review pending updates that require manual action. Use backups before major upgrades to prevent data loss. For teams, integrate update tasks into project planning, and assign clear owners for patch management. Encourage transparent reporting of issues and near misses to build collective knowledge. Finally, educate users about why updates matter and how they can participate in keeping environments safe and efficient.
Common Update Scenarios by Software Type
Different software types require tailored approaches. Operating systems often have automatic security patches, whereas applications may need version-specific compatibility testing. Open source components demand attention to licensing and ecosystem changes. Cloud services may push updates automatically, but customers should monitor service-level changes and deprecations. Desktop software can usually be updated with minimal disruption, but enterprise tools may need coordinated change management. Understanding these distinctions helps teams apply appropriate controls without slowing progress.
Scenario highlights:
- Operating systems require both security and feature updates.
- Enterprise applications benefit from staged rollouts and change management.
- Open source components should be reviewed for licensing and security fixes.
- Cloud services require monitoring of API changes and deprecations.
Measuring the Impact of Updates
Measuring outcomes helps justify update efforts and refine the process. Track indicators such as patch adherence rate, mean time to patch, and the incidence of post-update issues. User-reported problems, failure rates in automated tests, and system uptime before and after updates provide concrete evidence of impact. For security, monitor vulnerability disclosures and exploit mitigations that updates enable. Regular reviews of these metrics support continuous improvement and help demonstrate value to stakeholders. The goal is a predictable, secure, and high-performing software environment across all teams and users.
Your Questions Answered
Why should I keep my software up to date?
Keeping software up to date reduces security risks, fixes bugs, improves performance, and maintains compatibility with other tools. It also helps ensure you continue receiving vendor support and security advisories.
Keeping software up to date reduces security risks and fixes bugs, improves performance, and keeps you compatible with other tools.
What are the risks of delaying updates?
Delaying updates can leave systems vulnerable to exploits, cause software to crash or behave inconsistently, and lead to compatibility problems with other services. It can also result in higher remediation costs after a breach or outage.
Delaying updates raises security and stability risks and can lead to higher costs after problems occur.
How often should updates be applied?
Update cadence depends on the software type and risk profile. Critical security patches should be applied promptly, while less urgent updates can follow a scheduled window after testing and validation.
Critical patches should go in as soon as possible; other updates follow a planned, tested schedule.
Can updating software cause problems?
Yes, updates can introduce compatibility or performance issues. A staged rollout with testing in a safe environment helps catch problems before they affect users.
Updates can cause issues, so test first and roll out gradually.
What is patch management in a team?
Patch management is the coordinated process of identifying, testing, and applying patches across an organization. It reduces risk by ensuring consistent, timely updates across systems and applications.
Patch management is the coordinated process of applying patches across the organization.
Should I enable automatic updates for everything?
Automatic updates can protect systems, but critical environments may require controlled, audited deployment. Balance automation with policy and testing for high risk assets.
Auto updates help, but for critical systems you should test first and control the rollout.
Top Takeaways
- Automate updates where safe and schedule regular reviews.
- Prioritize patches by risk and impact rather than urgency alone.
- Test updates in staging environments before full rollout.
- Document and communicate update changes to reduce user disruption.
- Balance speed with thorough validation to maintain system stability.
- Track metrics to prove the value of patch management.
- Educate users on why updates matter to foster aligned practices.