What Happens When Software Is No Longer Supported
Learn what happens when software is no longer supported, including security risks, compatibility issues, and practical steps to migrate safely.
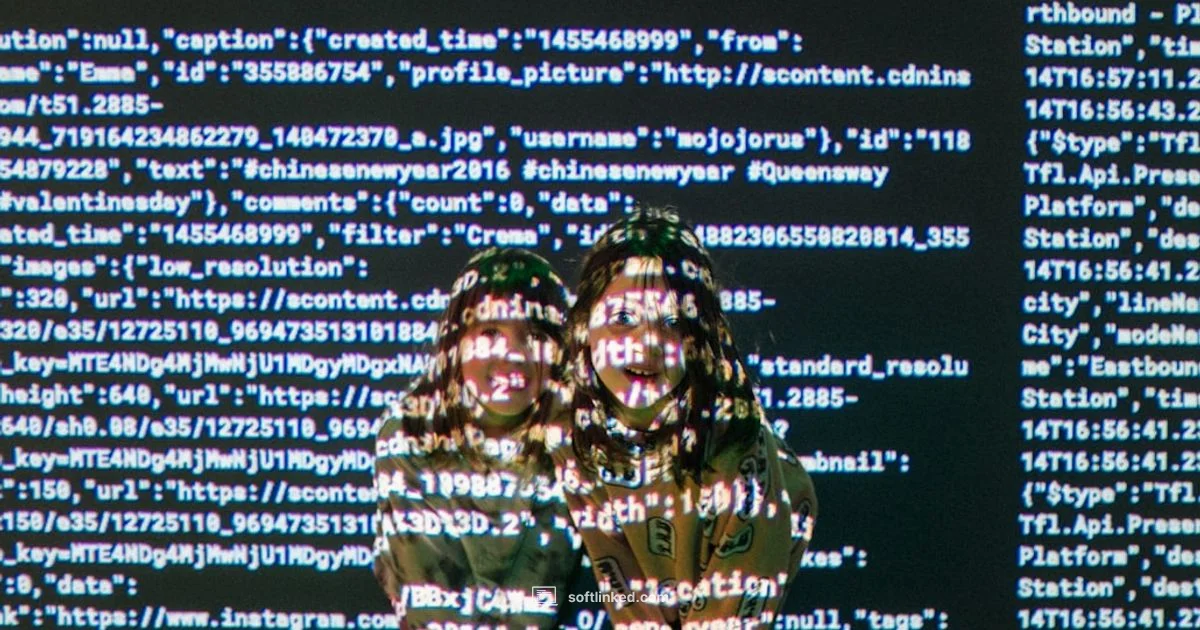
Software end of life (EOL) is the point at which a software product stops receiving official updates, patches, and vendor support.
What happens when software ends support
According to SoftLinked, software end of life marks a turning point for IT teams. When a vendor stops releasing updates, patches, or technical assistance, you inherit a growing surface area of risk and a shrinking window for safe operation. This moment is not merely about losing a feature or a new UI; it denotes a fundamental change in how you must manage the product. In practical terms, unsupported software stops getting security fixes, bug patches, and official troubleshooting help. That means known vulnerabilities remain unpatched, and new problems may emerge without official guidance. For developers and operators, the first consequence is a heightened attack surface and more frequent compatibility challenges with libraries, endpoints, and platforms that evolve over time. The SoftLinked team found that organizations often underestimate the cumulative costs of staying on old software, including emergency workarounds, ad hoc audits, and rushed migrations. The key takeaway is simple: plan early to avoid a crisis when support ends.
Security risks behind unsupported software
Security is the most immediate concern when support ends. Without patches, any newly discovered vulnerability can be exploited, and threat actors may tailor exploits to known flaws. This creates a higher risk of malware infections, ransomware incidents, and data breaches. In addition, many security controls rely on up-to-date software to function correctly, so intrusion prevention systems, anomaly detectors, and endpoint protections may become less effective. The absence of vendor guidance also means fewer official fixes or confirmed remediation steps during incidents. Organizations should treat this as a risk management issue, not just a technology problem. SoftLinked's analysis from 2026 underscores that relying on discontinued software increases exposure to risk over time and can lead to cascading problems across networks and applications.
Compatibility and maintenance challenges
As software ages, compatibility with new hardware, operating systems, and third party integrations deteriorates. New browsers, drivers, and cloud services may drop support for older interfaces, causing features to fail or degrade gracefully. Dependence on outdated components can complicate testing, continuous integration pipelines, and patch management. In many cases, teams must rewrite integrations or replace modules to maintain interoperability. The longer you delay, the more expensive a migration becomes, and the more likely you will encounter blocking issues during a move. The reality is that compatibility is not a one time hurdle; it evolves with every major platform update. This is why early assessment helps you map dependencies and prioritize critical upgrades.
Business and operational impacts
Unsupported software often translates into operational risks that affect uptime, compliance, and customer trust. Security incidents can trigger downtime, forcing costly incident response and recovery efforts. Compliance frameworks commonly require current patches and vendor support, so using outdated software can jeopardize audits and regulatory obligations. Maintenance teams may face escalating costs as they cobble together workarounds, pay for extended support, or hire specialists to patch or wrap the software. Decision-makers should also consider the opportunity cost of not migrating, including lost productivity, delayed feature delivery, and reduced competitiveness. In many organizations, the pressure to stay on old software is driven by fear of destabilizing critical systems; yet the real cost is often hidden in risk exposure and reputational damage.
How to mitigate risk before and after end of life
The most effective approach combines proactive planning with disciplined execution. Start with a complete software inventory, then assess risk by mapping dependencies, security impact, and business criticality. Create a migration strategy that prioritizes high risk and high impact components, and set a realistic budget with contingency for unforeseen blockers. Before ending support, run a pilot migration in a staging environment to validate compatibility and performance. After end of life, implement compensating controls such as network segmentation, stricter access controls, and enhanced monitoring to reduce exposure. Establish a clear incident response plan for potential breaches and ensure your team has updated runbooks and training. The goal is to minimize attack surface, maintain regulatory readiness, and preserve continuity while moving to a supported solution. SoftLinked Team notes that early planning reduces the cost and complexity of migration, making a difficult transition more manageable.
Alternatives to staying on unsupported software
If upgrading immediately is not feasible, there are interim strategies to reduce risk. Vendors sometimes offer extended security updates or paid extended support for a grace period, though these come at higher cost. In some cases, organizations can isolate the legacy system from sensitive networks, run it in a sandbox, or wrap it with security gateways. Virtualization and containerization can provide a controlled path to migration by decoupling software from hardware dependencies, but they are not a panacea; performance, licensing, and maintenance still require attention. Open source replacements or community-supported forks can be viable long-term options for certain workloads, provided there is an active roadmap and governance. The aim is to maintain control over security while buying time to complete a full upgrade.
Planning a safe migration path
A well-planned migration starts with a complete inventory of software, licenses, data flows, and user requirements. Next, identify dependencies, data mappings, and critical business processes that must continue uninterrupted. Build a robust test plan that replicates real production loads, and stage the migration in small, reversible steps to minimize risk. Establish rollback procedures, automation for repetitive tasks, and a clear ownership model across teams. Schedule training and documentation updates for users and operators. Finally, monitor post-migration performance and security, adjusting the plan as needed. A structured approach reduces downtime and increases the likelihood of a smooth transition to a supported platform.
Real world examples of end of life scenarios
Consider a mid sized company running a legacy CRM on an aging server stack that no longer receives updates. When a patch becomes unavailable, security gaps appear, and the team must decide whether to upgrade in place or migrate to a newer system. In another case, a university relies on an outdated classroom management tool that lags behind modern browsers and mobile devices. Teachers experience slower access to materials, and administrators face compliance concerns during audits. Both cases illustrate that waiting to act increases complexity and risk. The key lesson is that proactive planning beats reactive scrambling when support ends and transitions must happen quickly.
Long term considerations and best practices
To reduce risk over the long term, organizations should implement a formal software lifecycle program. This includes maintaining an up to date inventory of applications, defining support thresholds, and aligning budgets with planned upgrades. Regularly review vendor roadmaps, establish standards for secure configuration, and invest in staff training on migration tools and best practices. Build a governance model that approves changes, documents dependencies, and tracks progress against milestones. Continuous improvement means revisiting the lifecycle plan each year and adjusting for new security threats, regulatory changes, and technology trends. The SoftLinked team recommends treating end of life as a standard project risk, not a sudden crisis, and to maintain a clear, auditable migration path for every critical system.
Your Questions Answered
What does it mean for software to be no longer supported?
No longer supported means the vendor stops releasing security patches, bug fixes, and official assistance. You must assume responsibility for maintenance and migration planning.
When software is no longer supported, updates stop and you need a plan to migrate or secure your systems.
What risks come with using unsupported software?
The main risks are unpatched security vulnerabilities, regulatory non compliance, and potential system outages. You may also face compatibility problems with newer hardware or software.
Security risks and compliance issues rise when software is unsupported, and compatibility may break with newer tech.
How can I tell if my software is nearing end of life?
Check vendor lifecycle pages, product announcements, and renewal options. Subscribe to alerts and review support calendars for critical dates.
Look for official lifecycle notices and renewal timelines from the vendor.
What should I do if upgrading immediately isn't possible?
Develop a risk mitigation plan, isolate the system, and consider extended security updates or third party maintenance if available. Plan a staged migration when feasible.
Isolate risky systems and consider extended support while you plan a staged upgrade.
Are there compliance implications of using unsupported software?
Yes. Many standards require current patches and supported platforms. Using outdated software can complicate audits and regulatory reports.
Unsupported software can jeopardize audits and regulatory requirements.
How do I plan a safe migration path to a supported platform?
Start with an inventory and risk assessment, map dependencies, test in a staging environment, and roll out in manageable phases with rollback options.
Begin with inventory and testing, then migrate in well controlled phases.
Top Takeaways
- Identify end of life early to reduce risk.
- Prioritize security patches and compliance during migration.
- Map dependencies to plan a smoother upgrade.
- Test migrations in staging before going live.
- Engage stakeholders and budget for the transition.