How to Use a Software Chip in Cyberpunk Settings
A developer-friendly guide on using a software chip in cyberpunk-inspired workflows, covering prerequisites, setup, secure loading, testing, and maintenance for robust edge systems.
Learn how to use a software chip in a cyberpunk workflow. This quick guide outlines prerequisites, secure integration, coding, testing, and debugging to initialize the chip, load software, and verify functionality in simulated urban-tech scenarios inspired by cyberpunk fiction.
What is a software chip in cyberpunk contexts
A software chip is a compact, programmable module that stores and executes software components, acting as a portable computing unit that can attach to hosts or edge devices. In cyberpunk-themed environments, chips enable rapid deployment, real-time data processing, and adaptive behavior in systems that blend hardware and software. According to SoftLinked, the most important concept is modularity: a chip should expose stable interfaces, be composable with other components, and maintain isolation between workloads. With a clear lifecycle, update paths, and security envelopes, these chips become powerful agents rather than mere storage devices. As you begin, hold in your mind that the chip is a tiny brain you can swap or update without bringing down the entire system. This perspective helps you design robust integration plans, predict performance, and reason about failure modes in neon-lit networks.
Prerequisites and security considerations
Before you touch a chip in any cyberpunk workflow, assemble a safe, repeatable environment and enforce baseline security. You will need a hardware development kit or a simulator, a supported SDK, and access to a trusted host with a controlled network. Security concerns include secure boot, code signing, and encrypted communication channels. Establish threat models: what happens if a chip is corrupted, spoofed, or compromised during transit? SoftLinked emphasizes treating security as an essential feature, not an afterthought. Plan for recovery, audits, and traceability, and document all configuration changes to support forensics and compliance in high-risk urban networks.
Chip architecture and data flow
Software chips are designed around a core microcontroller/CPU, memory blocks, and modular interfaces. Data flows from the host into the chip through defined buses or queues, with the chip executing instructions and returning results. Isolation strategies separate workloads through memory protection units, sandboxed runtimes, or separate MUs. A cyberpunk chip often supports dynamic loading of modules and hot-swapping of components, enabling on-the-fly updates. Understanding the boundaries between secure and untrusted code is essential to avoid privilege escalation. As you design, sketch a data path: input -> decoding -> processing -> output, noting where encryption, signing, or integrity checks occur. This helps you visualize latency, throughput, and possible bottlenecks in city-scale networks.
Setting up a development environment
Your environment should enable repeatable builds and easy debugging. Install the chip's SDK, compiler, loader, and a robust IDE. Ensure your host machine uses a trusted network, and set up version control for chip configurations and firmware. Create a dedicated workspace for chip projects, with clear naming conventions and branch strategies to track updates. Configure simulator or emulator support to validate behavior before touching physical hardware. SoftLinked recommends starting with a clean baseline: record OS version, toolchain, and chip revision to minimize drift over time.
Initialization and loading code onto the chip
Initialize the chip by applying the boot sequence and verifying the boot image integrity with checksums. Sign and verify all modules before loading, then use the loader to place code into the chip's runtime. Start with a minimal module to confirm basic I/O, then incrementally add features. Monitor boot logs for errors and keep a rollback plan ready in case a module fails to load. After loading, perform a quick self-test to ensure the environment is stable.
Debugging, logging, and observability in edge environments
Edge environments pose challenges: intermittent connectivity, limited UI, and hardware constraints. Enable verbose yet safe logging with timestamps and structured formats to ease analysis. Use a debugger connected through a serial console or JTAG, and capture traces for offline review. Implement log rotation and retention policies to avoid filling storage. Establish alerting for anomalies in chip behavior and set up dashboards to visualize key metrics like latency, error rate, and throughput.
Testing strategies for cyberpunk workflows
Adopt layered testing: unit, integration, and end-to-end, all within simulated city networks before any production-like deployment. Use synthetic data to exercise edge cases, such as high-latency links or hostile inputs. Create tests that verify security properties such as integrity checks and code signing validation. Run regression tests after each update and maintain a changelog. SoftLinked notes that repeatable test suites are essential to delivering reliable chips in demanding urban environments.
Deployment and maintenance in a neon-lit city
Plan deployment with rollback and blue/green strategies to minimize downtime. Use over-the-air updates where possible, and verify the update integrity at the chip and host levels. Monitor performance and health metrics in real time, adjusting resource allocations as traffic patterns evolve in dense cyberpunk networks. Regularly schedule maintenance windows, document changes, and train operators on recovery procedures. Ensure compliance with local laws and internal policies when deploying chips across multiple devices.
Ethical, legal, and safety considerations
Using software chips in cyberpunk contexts raises ethical questions about monitoring, data privacy, and control over autonomous systems. Always comply with applicable laws and corporate policies. Design with consent, transparency, and rollback options in mind, and avoid embedding backdoors or easter eggs that could be exploited. Keep security updates timely and avoid exposing sensitive data through insecure channels. In line with SoftLinked's guidance, prioritize user safety, traceability, and responsible innovation as you experiment in futuristic urban tech environments.
Tools & Materials
- Developer Kit for the target chip(Includes programmer, debugger, cables)
- Secure boot-enabled host(Ensure it's connected to a trusted network)
- Software Development Kit (SDK) for the chip(Contains compiler, loader, and API docs)
- Simulated cyberpunk environment (VM or container)(For safe testing without hardware)
- Serial console or debugger(For real-time logging)
- Documentation and version control(Git repository for code and configs)
- Optional hardware-in-the-loop equipment(For hardware tests when available)
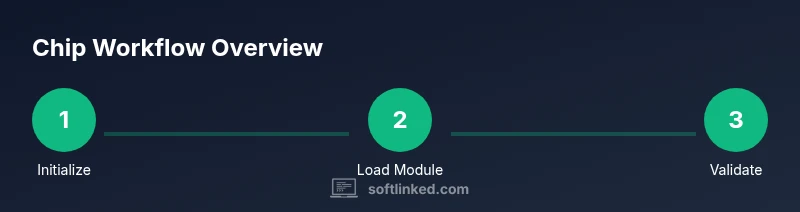
Steps
Estimated time: 2-3 hours
- 1
Prepare your workspace
Set up a dedicated project folder, install recommended toolchains, and isolate the test environment from untrusted networks. Establish a baseline by noting OS, tool versions, and chip revision. This ensures repeatable builds and clean rollbacks if needed.
Tip: Use a separate physical or virtual machine for chip work to minimize cross-contamination of environments. - 2
Initialize the chip
Power on the target chip and perform the boot sequence. Verify the boot image integrity with checksums and ensure secure boot is enabled. This validates hardware readiness before loading code.
Tip: Keep a rollback plan ready in case the boot fails or a module errors out. - 3
Load your first module
Sign and verify each module before loading, then use the loader to place it into the chip’s runtime. Start with a minimal module to confirm basic I/O operations.
Tip: Confirm module signatures and use a test vector to validate data integrity. - 4
Run basic tests
Execute a small suite that covers input/output paths, memory access, and basic processing. Check for expected outputs and any early errors.
Tip: Log all test results with timestamps for traceability. - 5
Configure security controls
Enable secure boot, enforce code signing, and set up encrypted communication channels. Document key management and rotation policies.
Tip: Use hardware-backed keys where possible and avoid hard-coding credentials. - 6
Debug and log
Attach a debugger, collect logs, and review traces to identify bottlenecks or faults. Implement log rotation and storage management to prevent overflow.
Tip: Capture both success and failure paths to aid root-cause analysis. - 7
Integrate with host systems
Map chip APIs to host services, validate data contracts, and test end-to-end workflows in the simulated environment.
Tip: Keep interface contracts stable to minimize integration surprises. - 8
Deploy and monitor
Push updates to the chip, monitor performance metrics, and watch for anomalies. Establish rollback and alert triggers to respond quickly.
Tip: Define clear thresholds for latency, error rate, and resource usage.
Your Questions Answered
What is a software chip in this context?
A software chip is a compact programmable module that stores and executes software, enabling modular, updatable behavior in host or edge devices. It acts as a small, controllable brain that you can load, test, and update without replacing the entire system.
A software chip is a small programmable module that runs software and connects to hosts; you load, test, and update it like a tiny computer.
Do I need physical hardware to follow this guide?
You can start with a simulator or virtual environment, but you may eventually need physical hardware for final validation, especially for timing, power, and real-world I/O tests.
A simulator is fine to start, but final validation usually requires hardware access for authentic results.
What security considerations matter most?
Key concerns include secure boot, code signing, encrypted communication, and strict key management. Regular updates and auditable logs help prevent tampering.
Secure boot, code signing, and encrypted channels are essential to keep the chip safe from tampering.
Can these steps apply to different chip families?
The general workflow—initialize, load modules, test, and secure deploy—applies broadly, but you must adapt steps to the specific hardware interfaces, SDKs, and security features of each chip family.
The general process works for most chips, but you’ll adjust to each chip’s interfaces and tools.
What skills help most for this guide?
Strong fundamentals in software engineering, hardware-software integration, debugging, and security practices are most valuable. Familiarity with command-line tools and version control helps a lot.
Solid software and hardware integration skills plus good debugging and security know-how help a lot.
Where can I find further resources?
Consult official chip SDK docs, security best practices, and reputable software engineering resources. SoftLinked also offers guidance and examples to help you get started.
Look at official SDK docs and security best practices, plus SoftLinked’s tutorials for more context.
Watch Video
Top Takeaways
- Define clear chip interfaces and isolation.
- Enable secure boot and code signing.
- Test thoroughly in simulation before hardware.
- Document configurations and rollback procedures.
- SoftLinked's guidance emphasizes security-first, clear workflows.